The Invisible Power of Public Data
Imagine a world where intelligence isn’t gathered in dark rooms with hidden microphones, but in broad daylight — through tweets, weather data, and company press releases. Welcome to OSINT, short for Open Source Intelligence.
If the old spies relied on trench coats and dead drops, today’s intelligence communities rely on Wi-Fi, Google, and a decent cup of coffee. OSINT stands for a simple yet world-changing idea: you can gather and analyze publicly available information to produce actionable intelligence — insights that can prevent cyberattacks, uncover corruption, or even help find missing people.
And here’s the fun twist: you’ve probably used OSINT yourself. Ever checked someone’s LinkedIn before a meeting? Googled a phone number? Congratulations — you just used open-source intelligence techniques on a micro scale.
Now let’s zoom out to the professionals who do it for national security, cybersecurity, and investigative work — and see how this discipline evolved from a niche craft to a global intelligence powerhouse.
From Radios to Algorithms – The Evolution of OSINT
The term open source intelligence sounds modern, but the roots go way back.
During World War II, analysts monitored public radio broadcasts and foreign newspapers to understand enemy movements. That was early OSINT — listening to what was already “in the open.”
Fast-forward to the digital age: information exploded. The internet turned every individual into both a source and a broadcaster. Suddenly, open source information wasn’t just in newspapers — it lived in tweets, code repositories, satellite images, and even restaurant reviews.
By the 1990s, intelligence agencies realized that open data could reveal patterns faster than many classified sources. OSINT began shaping military and diplomatic decisions. By the 2020s, as cyber threat intelligence grew in importance, OSINT became the foundation of intelligence for security worldwide.
Today, organizations use OSINT to map threat actors, detect vulnerabilities, and understand geopolitical risks in real time. What began as radio monitoring now fuels billion-dollar defense systems and corporate security operations.
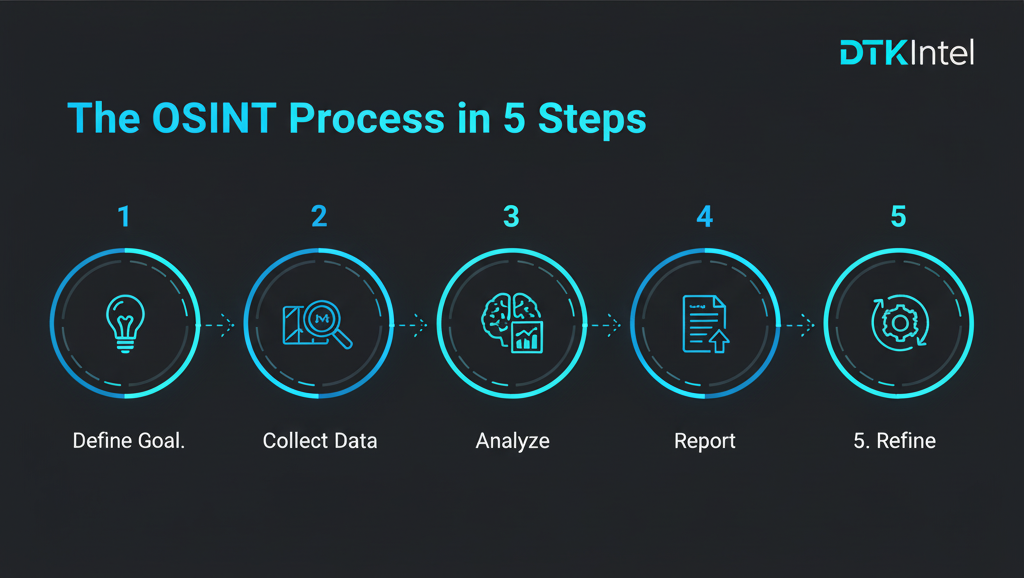
How OSINT Works – From Curiosity to Intelligence
At its heart, OSINT is about gathering intelligence from open, legal, publicly available data for intelligence purposes.
But don’t picture someone typing random keywords into Google. Modern OSINT is a disciplined, methodical process that turns chaos into clarity.
Step 1: Define the Mission
Every OSINT investigation begins with a specific intelligence need.
Maybe a company wants to check if its confidential data was leaked.
Maybe a government agency needs to identify disinformation networks before an election.
Or maybe a journalist wants to verify a viral video’s location.
Without a clear purpose, you’ll drown in data. So the first step is always to address a specific intelligence requirement — what do you need to know, and why?
Step 2: Collect From Open Sources
Once the mission is clear, analysts use open sources:
- News sites and blogs for situational awareness.
- Social media platforms for social media intelligence (SOCMINT).
- WHOIS and DNS records for domain investigations.
- Government and corporate databases for open-source information on ownership or funding.
- Leaked datasets and dark-web mirrors for security posture assessments.
Collection involves both manual search and automation. Modern analysts use scraping tools, APIs, and frameworks like the OSINT Framework to organize hundreds of data sources efficiently.
Step 3: Process and Clean the Data
Raw data is messy — duplicates, noise, contradictions. Analysts filter, tag, and normalize information to build a structured dataset. AI-based analysis tools now help detect correlations across massive datasets, improving the intelligence collection process.
Step 4: Analyze and Interpret
Here’s where art meets science. Analysts gather and analyze data to identify patterns, connections, or anomalies. For instance, finding that several fake social-media accounts share identical posting times could reveal a coordinated influence operation.
The goal is to generate actionable intelligence — something decision-makers can use. A clean spreadsheet means nothing if it doesn’t lead to action.
Step 5: Report and Refine
Finally, the intelligence is presented: graphs, visuals, and concise reports that tell a story. OSINT can also be active OSINT, meaning analysts continuously monitor a situation and update findings. Then, like any living process, OSINT loops back — what worked, what didn’t, what needs deeper digging.
That’s the step in the OSINT process that separates amateurs from professionals: iteration.
Real-World Example: Hackers Use OSINT Too
Before you assume OSINT is only for the “good guys,” let’s face the uncomfortable truth — hackers use OSINT all the time.
Before launching an attack, they collect OSINT data about targets: exposed emails, open ports, leaked credentials, social-media habits of employees.
Ironically, the same tools and techniques used by security analysts are also used by adversaries. The difference lies in intent.
Security teams use OSINT to strengthen their security posture, while attackers use it to exploit weaknesses.
That’s why understanding OSINT isn’t optional anymore — it’s the first step toward defending yourself in the modern realm of intelligence gathering.
Tools of the Trade – Turning Curiosity Into Capability

The OSINT world is packed with tools and techniques that help analysts collect and make sense of data. Here’s a peek inside that toolbox:
- Maltego: A visual link-analysis platform that maps connections between entities.
- SpiderFoot: An automated open source intelligence gathering tool scanning everything from IPs to social networks.
- Shodan: The search engine for open ports and connected devices.
- The Harvester: Collects email addresses and subdomains for intelligence for security assessments.
- Wayback Machine: Retrieves deleted web content — gold for investigators.
These open source intelligence tools and frameworks help organizations conduct comprehensive threat intelligence and expose hidden digital risks.
But remember: tools don’t make the analyst. A hammer doesn’t build a house; it’s the carpenter’s technique that matters. Similarly, effective OSINT depends on applying best practices, not just running scripts.
OSINT in Cybersecurity and National Security
Let’s get concrete. How does OSINT actually change the world?
In cybersecurity, OSINT enables organizations to use open source intelligence for continuous monitoring. By collecting publicly available data for intelligence, teams can identify exposed assets, detect phishing domains, and even anticipate ransomware attacks.
For national security, OSINT provides early warning signals. Intelligence agencies often use OSINT to perform threat mapping, spotting shifts in political sentiment or military movement through open data.
During the early phase of the 2022 war in Ukraine, online analysts used social media intelligence and satellite images to track troop movements — sometimes faster than official channels. That’s OSINT in action.
In both worlds, OSINT provides something unique: transparency. Unlike proprietary intelligence sources, which are classified, open data allows for public verification — a cornerstone of modern democratic accountability.

Ethics and the Human Side of OSINT
Here’s where it gets tricky. Just because data is “open” doesn’t mean it’s free to exploit without thought.
Professional analysts follow ethical OSINT standards: respecting privacy, protecting victims, and maintaining neutrality.
Responsible OSINT practices ensure that collection methods don’t violate laws or cause harm. For example, scraping public social-media data about protestors could endanger lives if shared irresponsibly.
There’s also the question of unlike proprietary intelligence, OSINT can expose personal data unintentionally.
So, ethical guidelines and OSINT best practices are critical — validating sources, obtaining consent when necessary, and keeping data secure.
Ultimately, OSINT is only as good as the integrity of its practitioners.
Beyond the Acronyms – How OSINT Really Feels in Practice
Ask any OSINT practitioner what a day looks like, and they’ll tell you it’s part detective work, part digital archaeology, and part caffeine dependency.
You might start by checking sources of OSINT — Twitter threads, government databases, academic journals. Then dive into metadata, cross-reference company IDs, or analyze how a viral video’s shadow angles confirm its location.
Sometimes you strike gold. Sometimes you chase dead ends for hours. But when everything clicks — when data from five open sources aligns perfectly — that’s the magic. That’s when you realize OSINT can also solve cases others thought impossible.
The Broader Context of OSINT
To learn how open source intelligence shapes our world, you need to see its context.
Governments use it for transparency and accountability. NGOs use it to document human-rights abuses. Businesses use it to manage reputation risks. Even individuals use OSINT to verify fake news before sharing it.
It’s a toolset that crosses borders — part of a larger realm of intelligence gathering that includes signals intelligence, human intelligence, and now artificial intelligence. Each discipline supports the others.
In that way, OSINT isn’t just data collection; it’s a mindset — curiosity structured into a process. It ensures that OSINT works not by accident, but through consistent application of logic and ethics.
How AI Is Changing the Game
Here’s the new frontier: AI and advanced threat intelligence.
AI doesn’t replace OSINT — it supercharges it.
Machine learning algorithms now help analyze OSINT data, spot anomalies, and correlate vast datasets at superhuman speed. Large-language models assist analysts by summarizing reports, identifying entities, and suggesting specific intelligence needs to explore.
This evolution of OSINT means future analysts will combine automation with human intuition — creating hybrid intelligence systems where machines handle volume and humans handle meaning.
But here’s the caveat: AI can hallucinate. The human analyst remains the final gatekeeper of truth. OSINT still depends on human reasoning, ethical judgment, and contextual awareness.
Case Study: When OSINT Changed the News
In 2018, a group of independent investigators from Bellingcat used open source intelligence gathering to identify the suspects in the Skripal poisoning — using nothing but flight logs, leaked databases, and facial comparison from social media.
They didn’t hack a single system. They simply used open source intelligence with precision and discipline. Their work later forced official agencies to confirm identities they’d initially denied.
This single case redefined how the world viewed OSINT: as a source of information so powerful it could rival traditional espionage — but transparent enough for anyone to verify.
The Future of OSINT
As we move deeper into a data-saturated world, OSINT will become even more essential.
- Many OSINT tools will integrate directly into threat intelligence platforms, automating risk detection.
- Governments will rely on open source intelligence techniques to counter misinformation.
- Companies will invest in OSINT teams to secure brand reputation and security vulnerabilities.
- Training programs will emerge to teach tools and techniques used in ethical OSINT collection.
And yes — hackers will keep adapting, which is why defensive OSINT must evolve just as fast.
In short, OSINT enables organizations to see what others overlook — transforming noise into foresight.
Conclusion – Why Everyone Should Care About OSINT
OSINT stands for Open Source Intelligence, but in truth, it stands for something larger: empowerment through knowledge.
When done right, it ensures that intelligence is used responsibly, that transparency thrives, and that truth remains accessible.
It’s not only a discipline for spies and analysts — it’s a lens through which we can all understand our hyperconnected world.
Open-source intelligence reminds us that information is power — and that in the 21st century, power belongs to those who can interpret the open web, not just those who control it.
So the next time you scroll, search, or analyze — remember, you’re walking through the same digital streets where modern intelligence operates.
And if you master OSINT’s techniques and tools, who knows?
You might not just find information — you might change the way people see the world.

